Transfer To iPhone 17

MobileTrans App
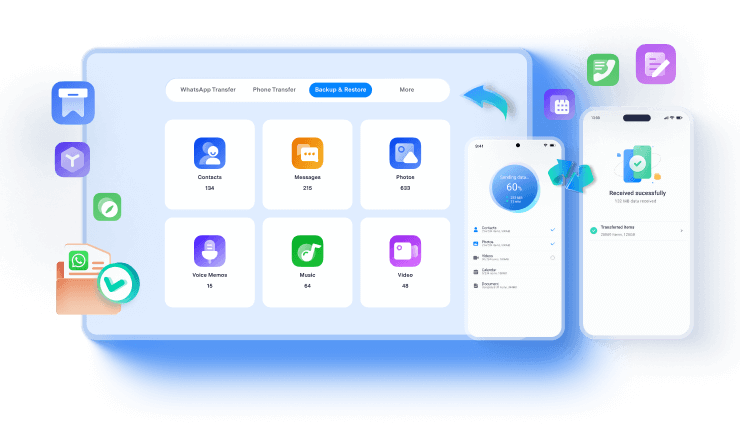
Effortlessly transfer your phone data and keep your memories intact!
It's a higher priority than any time in recent memory to ensure personal information protection with your mobile gadgets being secure and your data staying private. Recall the days when cybercriminals principally used their raids around PC and laptops?
Times appear to be evolving. Today, cybercriminals are focusing on cell phones and tablets regularly. It makes everyone wonder which mobile OS is safer, Samsung vs. iPhone, or one may say Android or iOS?
The iOS and Android have become enticing focuses for cyberthieves anxious to get to the data and privacy of consumers. If privacy is your concern, and you need to keep your Android or iOS free of such attacks, which OS would it be a good idea for you to pick? Here, we have provided a thorough guide to help you choose the best phone manufacturer among the Samsung vs. Apple battle.
Data Privacy Week, celebrated worldwide from January 24 - 28, is a global work to educate people about data privacy. It tells us how different organizations utilize and take advantage of our data. The reason advocates regarding the privacy of people, and for companies to be more straightforward with regards to how they handle client data.
Background of Data Privacy Week
In 1981, the very first global treaty that discussed data privacy and its security was shaped by the Council of Europe. It protected the privileges to the privacy of clients.
To celebrate the marking of Convention 108, Data Protection Day was made on April 26, 2006, with the date of the recognition set on January 28. In 2022, the yearly holiday will extend to a week-long mission called Data Privacy Week.

Purpose of Data Privacy Week
Data Privacy Week instructs people about internet-based privacy, how to distinguish whether their data is being utilized, and what measures they can take. The holiday urges organizations to quit manipulating data gathered and be responsible for the user data collected.
Truth is:
Every internet-based step we do leaves an imprint. Regardless of whether it is a person's online action, website visits, or individual data, for example, ID numbers, it is gathered and shared without the client's command. It turns out to be progressively vital to deal with and secure your data on the web. We urge everybody to be careful with their privacy settings, passwords, and where they are using their essential data, just like the GDPR cyber security.
Apple's iOS has been viewed as the safer of the two OS for quite some time.
Here's why:
iPhone Data Protection

Samsung Data Privacy
There is an application audit process for Google Play, but sadly, the process is not as tough as what they face while adding applications to Apple's App Store. It's easy for harmful apps to sneak onto the Google Play store and effortless for people to download one. One of the fundamental issues is that the end-user can even download an application from Unknown Sources. That implies you can download apps on your phone that are not recognized by the Google PlayStore. The APK, as it's called, can be installed directly from Google without having passed the Google PlayStore review criteria.

Samsung Galaxy S22 (Ultra): The Most Anticipated Phone Model
Samsung's gigantically famous Galaxy S cell phones are without a doubt the nearest competitor to Apple's iPhone, and the S22 series is the following model of phones to show up this year. With deals gradually declining for the S-series leads, the S22 line puts everything on it, and Samsung ought to put it all out there to demonstrate that it makes the best Android phones. It is the most anticipated phone of the year since Samsung will be doing many redesigns for their new model. The Samsung Galaxy S22 Ultra will turn into the most impressive one in the series, and we're here to see it. We've, as of now, shared reviews for the Galaxy S22 and S22+ and all the upcoming models.
What's more:
The Galaxy S22 Ultra will not be the same as its previous model in various ways. It will have a better camera, display, design, processor, and battery, all at an equal or lesser price tag than the previous model, i.e., Galaxy S21 Ultra. Samsung says that the S22 Ultra is going to be the next generation's Note.
After getting a new phone, there are a couple of things you should do before putting it to use.
Here's what to do:
After the phone passes your visual assessment, begin charging it. Keep your telephone switched off and allow it to get charged for an entire eight hours.
If your new phone drops cellular connection and fails to make a connection with the mobile network or drops it effectively, then, at that point, the rest doesn't make any difference.
You can look at this by moving to the spots where your old telephone would drop calls. Assuming it drops calls sooner than the old telephone, it probably won't be so great. Remember, cell signals fluctuate in strength, in any event, when you are in a similar spot.


Capture a few pictures with every one of the cameras on the phone and in every one of the modes conceivable; photo, video, panoramic, slow-mo, etc., whatever modes it has. Do the images emerge as they ought to? Do every one of the methods of capturing an image work, such as physically clicking the on-screen button or the volume (up/down) button?
Ensure that your new telephone will catch WiFi connections and Bluetooth gadgets and keep it connected over a suitable distance. It should remain connected with your WiFi anyplace in your home or keep Bluetooth devices connected.
Since the cell phone is an electronic expansion of our lives, it is essential to protect its security. The way that we have everything, from our family photographs to government ID to bank cards put away on our phones, makes them a valued objective for hoodlums.
Put the highest level of safety on it that you can. For most phones, that implies setting up a password or screen lock pattern. At long last, make your mobile damage-proof. Get a decent case for it to shield it from knocks and falls. It will not be very effective, yet it will assist in maintaining the phone until it's the ideal opportunity to upgrade it.
Moving up to a new phone sounds engaging until you think about the data there in your handset. From photos and recordings to a large number of instant messages, your phone is a virtual treasure. Be that as it may, Wondershare MobileTrans makes it a breeze to those data. MobileTrans distinguishes your telephones and tells you exactly how much data you have to move.
But here's the good part:
MobileTrans lets you transfer all types of data between two phones regardless of which network they use, as long as you have a PC. Bringing over the entirety of your different data, for example, pictures, call logs, and messages, is easy, particularly if you're changing phone company. Apps can also be moved distinctly between compatible gadgets using MobileTrans. With MobileTrans, you need to connect both phones to your PC, and you're good to go.
Check our video tutorial below:
This article provides detailed information on which phone is better for Samsung and iPhone. We have distinguished Samsung data protection from iPhone's privacy to decide which phone is better in data privacy. Along with that, if you are looking to buy a new phone, consider using MobileTrans to transfer your data to the new mobile phone. After reading this article, we hope you will decide which phone provides better security among Samsung and iPhone.
New Trendings
Top Stories
All Categories
Axel Nash
staff Editor